Tag: GIlles de Kerchove
-
Action plan on Afghanistan: Europol to hire evacuated staff from Kabul

A high-ranking EU advisor has drawn up recommendations for the Council and the Commission on how to deal with evacuees and refugees from Afghanistan. The focus is on more cooperation with secret services and NATO. The European Union’s anti-terrorism coordinator…
-
Quitting EU adviser: Gilles de Kerchove invents “left-wing terrorist” threat

A handful of property damages in Italy could lead to left-wing activism being pursued more closely by police and secret services across the European Union. The initiative bears the hallmarks of the German Office for the Protection of the Constitution.…
-
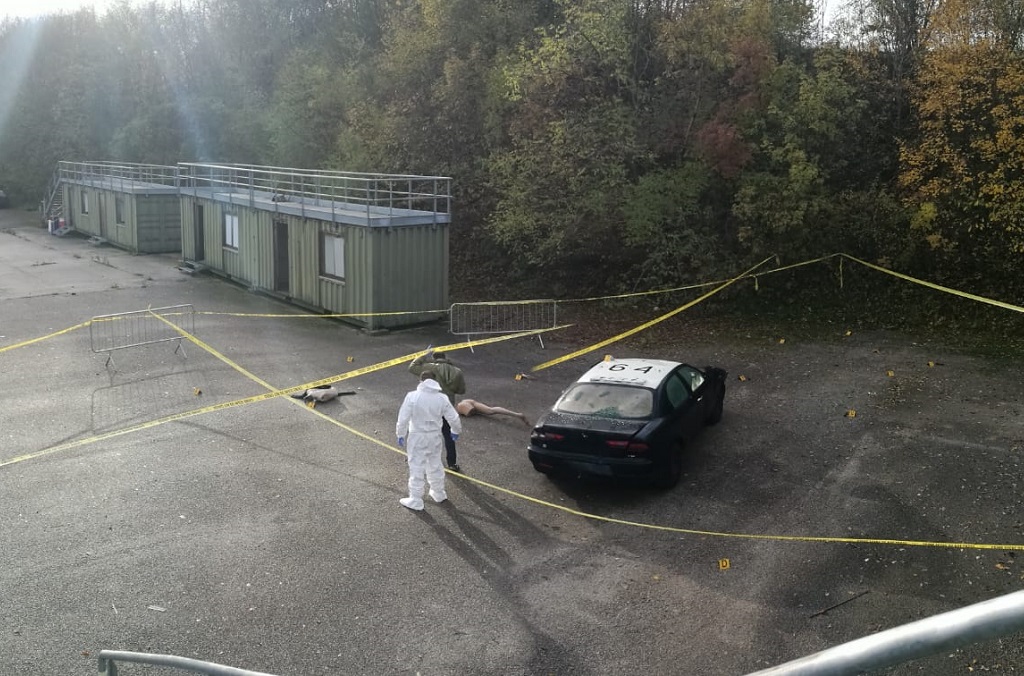
“Battlefield information”: EU police to cooperate more closely with secret services and military
Authorities in the European Union use biometric data and crime scene evidence from Iraq and Syria to process war crimes, secretly track suspects and control migration. Now the procedure is to be extended to African countries. After a meeting of…
-
Council and Commission: EU seeks two high-level security coordinators

After 14 years, the Council wants to recruit a new Counter-Terrorism Coordinator. Her remit will be expanded to include hybrid threats and cybersecurity. The Commission is also creating such a post. The member states united in the European Council want…