Tag: Trojans
-
Restrictive in cyberspace

New German cybersecurity guidelines harbour even more surveillance and centralised powers The Federal Cabinet today approved the new “Cybersecurity Strategy for Germany”. The draft, prepared by the Federal Ministry of the Interior, is to be in place for five years…
-
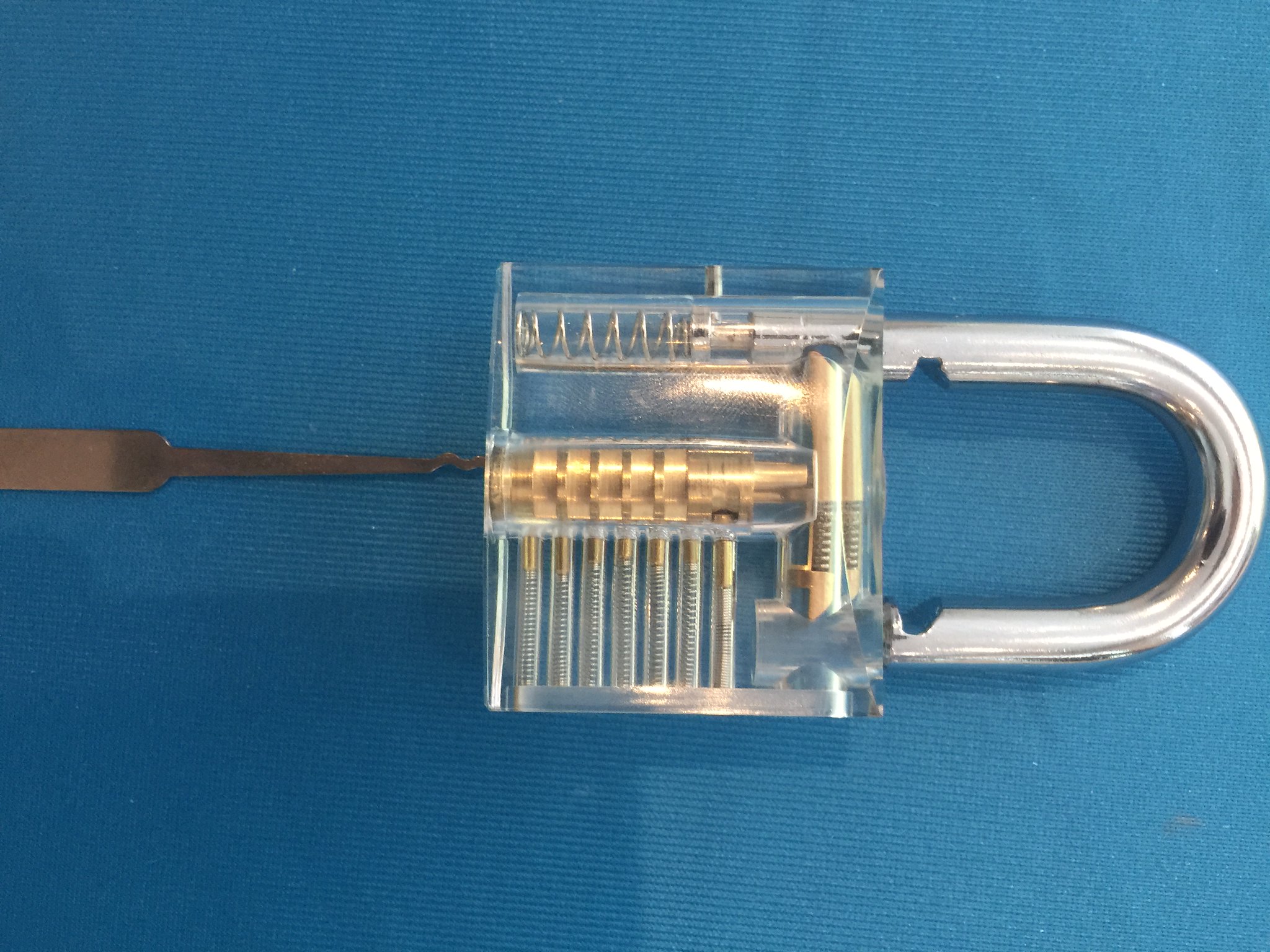
Spotlight on: State Trojans

In Greek mythology, the horse outside the city of Troy was a wooden gift in whose hull some of the hostile Achaeans had hidden. Unsuspecting inhabitants, certain of victory over the invaders, pulled it in, the Achaeans climbed out at…
-
Germany: Trojans for all

The German Bundestag passed new wiretapping laws for secret services and the Federal Police In future, German secret services will be able to remotely access private computers or telephones with spy software. They will be allowed to intercept not only…
-
How it all began: Five years of fight against end-to-end encryption
The German EU Presidency wants to enable police forces and secret services to circumvent end-to-end encrypted communication or to use technical tools to defeat it. A look at the activities carried out over the past five years allows some conclusions…